Students have been taking to social media calling attention to the influx of phishing emails they have received in their student email inboxes.
Bryon Jackson, director of service management and operations, said the issue isn’t new.
“Phishing emails have become pretty commonplace,” Jackson said in an email. “We see attempts throughout the year, but our peak periods coincide with the fall and spring semesters, as more people succumb to phishing, the more reports we see.”
Scammers send these emails in attempts to secure sensitive information from its receivers.
“Our campus email system intercepts thousands of phishing emails daily. Some that slip through are further intercepted by email clients such as Outlook,” Jackson said. “Once a campus email user succumbs to a phishing attempt, we start to see more successful delivery of phishing emails as they are coming from a ‘trusted source.’”
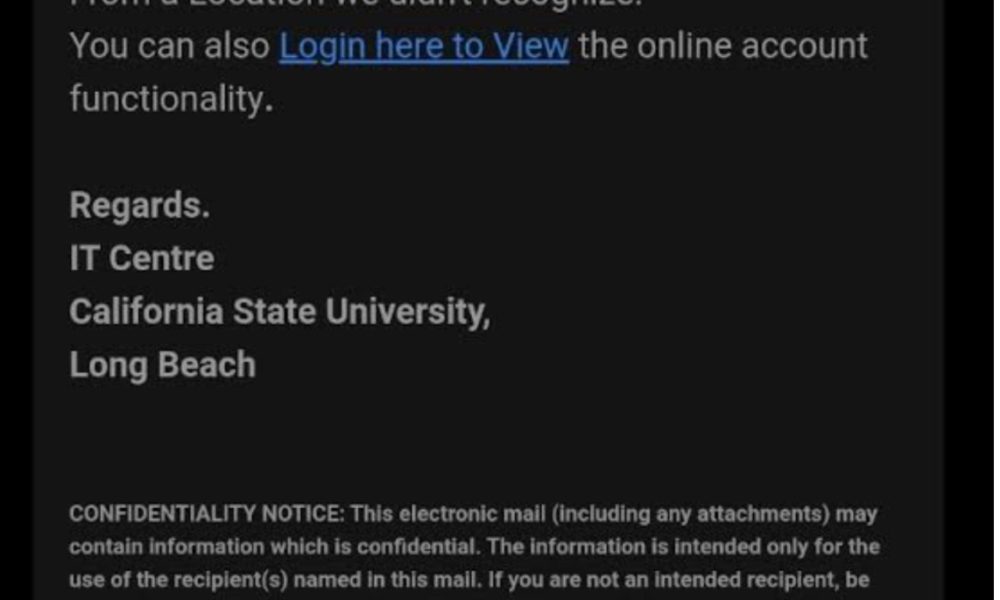
Christopher De Jong, third year computer science major, has become all too familiar with scam emails. He received a message from a sender claiming to be the “IT Centre” on campus.
“I might have a dozen or more [in my inbox],” Jong said.
Several other students who posted online had the same source for their emails. Jackson said this is a common scheme for scammers.
“When accounts become compromised, the hacker tends to send the same message out to thousands of email accounts within the same system,” Jackson said. “Hackers tend to slightly change the subject line and email text body, knowing IT organizations such as ours actively work to block known attempts, so you may see a few similar looking phishing messages from the same hacker.”
Jong knew immediately that the email was a scam, but others aren’t as aware of the threats associated with fishy emails.
Jackson said that phishers mainly gain access to servers when people respond to their emails.
“Typically, a student, or faculty or staff, responds to a phishing attempt by unknowingly providing the hacker with his/her credentials,” Jackson said. “Whether it be through a fake login screen or web form, the hacker captures the username and password of the compromised person, the hacker then uses those credentials to access the account to send more phishing emails.”
For most scammers, it only takes one email to start the widespread phishing students are experiencing at the moment.
“Once a campus email user succumbs to a phishing attempt, we start to see more successful delivery of phishing emails as they are coming from a ‘trusted source,” Jackson said.
The source of these emails is unclear, butJong feels that there may be a few possibilities.
“It may be a phishing scam, students doing a thesis or research from a professor or someone training an AI to create or detect these scams,” Jong said.
Jackson said that the possible origins of the emails are just as varied as Jong suspects.
“When we receive forwarded phishing emails, we review the email header information, which gives us a lot of detail regarding the email’s origin, including if the sender was a compromised account or if the email was spoofed,” Jackson said. “We’ve seen many cases where someone masquerades as a legitimate email account to trick people into providing them with something of value, such as gift cards or their credentials.”
In the case of being the recipient of a scam email, Jackson said the proper response is to just ignore it and reset the account information that the scam was sent to.
“If a campus email user suspects they provided their username and password, they should reset it immediately by visiting https://beachid.csulb.edu,” Jackson said. “Resetting the password is the most effective way to stop the hacker from accessing their account.”
Hannah Getahun, special projects editor, contributed to this article.